Call a Specialist Today! 877-352-0546
Call a Specialist Today! 877-352-0546
Free Shipping!
The convenience of being able to sign on just once and access many applications is a great reason to use single sign-on (SSO), but it’s not the only one. Single sign-on also means fewer access points, which reduces the vulnerabilities for cyberattackers to exploit.
You can improve identity security by combining SSO with other identity and access management capabilities. For example, you can use multi-factor authentication with SSO to require additional factors of authentication when the level of risk warrants it.
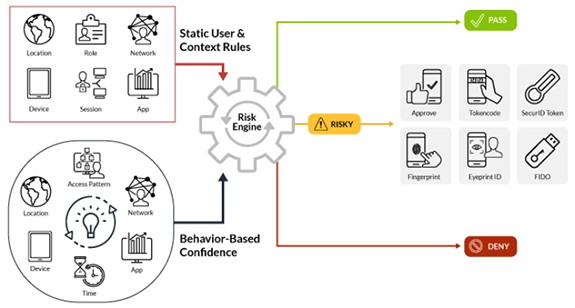
Risk-based authentication works with SSO to enhance the user experience by only stepping-up authentication factors if the level of risk exceeds what the organization has defined. The level can be based on variables such as who is requesting access, what they’re requesting, and where they’re located.
Policy-based access decisions are possible through the integration of SSO and identity governance. This integration ensures that SSO operations are always consistent with the organization’s established access management policies.