
RSA FraudAction Cyber Intelligence Service
Fraud Intelligence Services
Overview:
Get unprecedented insight into the cybercriminal underground and attacks targeting your organization. Our dedicated team of multilingual analysts monitors the underground forums, IRC chat rooms and other clandestine communication channels cybercriminals use.
- Deep undercover intelligence agents engage in this underground community.
- Intelligence capable of revealing the identities of threat actors behind attacks.
About the RSA Fraudaction Intelligence Operation
The RSA FraudAction intelligence operation is comprised of a dedicated team of analysts who monitor underground forums, IRC chat rooms, the open web (OSINT) and other communication channels where cybercriminals congregate to sell and buy services and tools and exchange knowledge.
Leveraging highly skilled, multilingual expertise and years of underground presence, RSA FraudAction analysts have been “grandfathered” into forums as trusted players. Our analysts cover activity in forums of different languages, including Chinese, Russian, French, Arabic, Spanish, Portuguese and others.
The forums vary in size, traffic volume and prestige. In many cases, the forums monitored by analysts are closed forums that require admission fees and “vouching” by a senior member(s). Some of the exclusive forums monitored by RSA are closed to new users and are considered by cybercriminals to be more secure exchange platforms.
RSA FraudAction Cyber Intelligence
RSA FraudAction Cyber Intelligence is offered in three distinct tiers of service, which vary in depth of content and coverage.
- TIER 1: General Intelligence
Primarily designed for organizations interested in feed-based, automated intelligence consumption. - TIER 2: Targeted Intelligence
For organizations that require the additional layer of proactive (human) investigation into deep-web sources. - TIER 3: Advanced Intelligence OPS
This tier includes all tier 1 and 2 deliverables with the addition of ad hoc, on-demand research.
| Comparison of Tier Offerings | Tier 1 | Tier 2 | Tier 3 |
|---|---|---|---|
| General | |||
| Threat Reports | |||
| IP Feed | |||
| Email Feed | |||
| E-Commerce Item Drops | |||
| Banking Mule Accounts | |||
| Targeted | |||
| Compromised Credit Cards | |||
| Credit Card Store Previews | |||
| Compromised Credentials | |||
| Brand-Specific Intel | |||
| Enterprise Blacklists: Malicious URLs | |||
| Advanced | |||
| On-Demand Research | |||
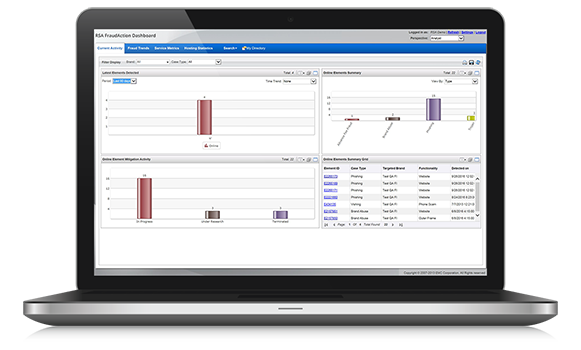
Features:
![]()
Tier 1: General Cyber Intelligence
Designed for organizations interested in feed-based, automated intelligence. Feeds are available in several formats and can be integrated into different back-end appliances/systems. The nature of intelligence is mostly general and includes complimentary access to threat reports that provide insight into emerging cybercrime threats and trends.
![]()
Tier 2: Targeted Cyber Intelligence
Designed for organizations that require an additional layer of proactive, human investigation into deep-web sources. Tier 2 includes all the features of Tier 1 in addition to highly-targeted threat feeds that relate directly to the organization’s brand.
![]()
Tier 3: Advanced Cyber Intelligence Operations
Offered to RSA FraudAction customers, Tier 3 provides comprehensive insight into threats targeting an organization’s brand and business operations via the ThreatTracker report. This report fuses intelligence gathered from phishing and malware attacks with our deep-web operation. It also provides visibility across attack vectors, attack clusters and the individuals behind these attacks. Tier 3 includes all Tier 1 and 2 deliverables in addition to unlimited, on-demand research.
Benefits:
- Coordinates and launches sting operations against cybercriminals to reveal their infrastructure and operations.
- Arms you with an intelligence-driven strategy for fraud prevention.
- Identifies cash-out and cross-channel exploits, mule accounts, item drops and other fraud-related entities.
- Enables you to stay up to date on cybercrime activity, emerging threats and fraud trends.
- Offers a flexible, three-tier approach to intelligence delivery ranging from automated intelligence updates to customized reports.
- Reveals the underground stores selling compromised online banking and payment card accounts.
Documentation:
Download the RSA FraudAction Cyber Intelligence Datasheet (.PDF)

